Radio Frequency Identification (RFID) technology operates by using electromagnetic fields to autonomously identify and track tags on various objects, such as access cards.
The Lintechtt F3 card dispenser is a standout example of this technology at work, showcasing how RFID can be effectively utilized in modern access systems.
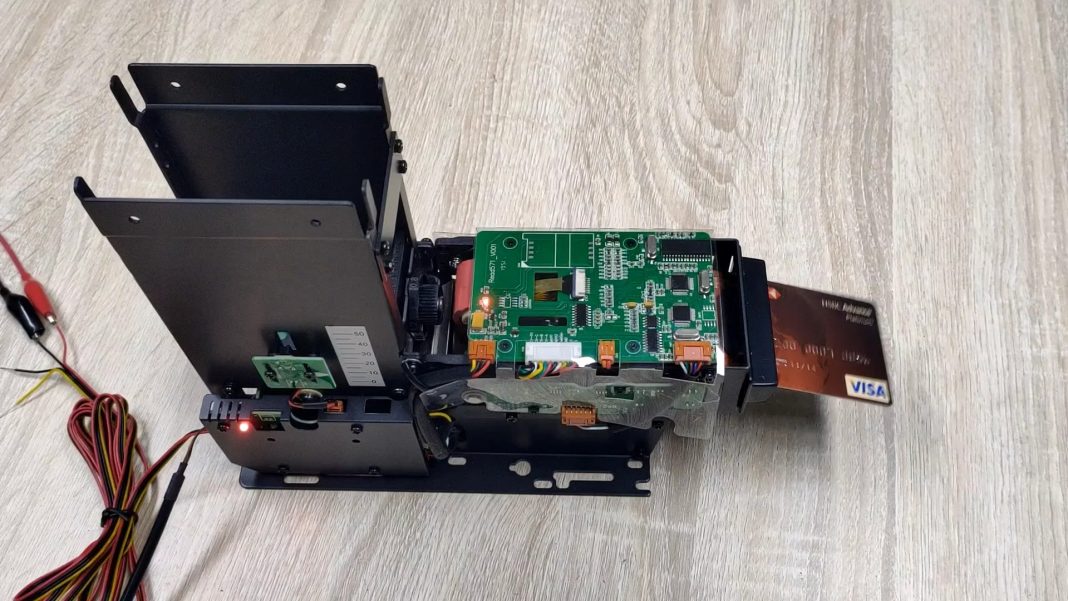
This state-of-the-art S50 reader card dispenser comes with integrated RFID technology to dispense and collect cards all the while reading and writing them per requirement.
However, to understand the proper impact of RFID technology in access control, we must discuss the comprehensive advancements in access control for the last few decades. So, let’s dive right into our discussion!
Lintechtt F3 Card Dispenser
The F3 card dispenser by Lintechtt is a standout in the realm of access control, boasting an impressive ability to read and write to RFID cards. This feature enables versatile and secure access management across various applications.
The dispenser’s innovative transfer wheel design guarantees precise and consistent card dispensing, adeptly handling cards with irregular surfaces. Its adaptability to various card thicknesses enhances its versatility, allowing it to accommodate a diverse array of card types with ease.
These innovative features underscore the F3 card dispenser’s role as a crucial component in modern access control systems.
RFID Technology in Access Control
RFID (Radio-Frequency Identification) technology employs electromagnetic fields to effortlessly identify and monitor tags. These tags can be bound to different objects such as access cards, order cards, etc.
In access control, this technology translates into enhanced security and operational efficiency. By enabling contactless identification, RFID systems reduce the time required for authentication and increase the ease of entry for authorized individuals.
They also bolster security by offering encrypted data storage on cards, making unauthorized access or duplication much more challenging. This combination of swift, secure verification is what makes RFID an invaluable tool in contemporary access control systems.
Integration of RFID Card Dispensers in Access Control Systems
The integration of RFID card dispensers, like Lintechtt’s F3 model, into existing access control systems marks a significant advancement in both security and operational efficiency.
These dispensers can seamlessly blend with current systems, providing a more streamlined and automated approach to access management. The advantages are manifold: enhanced security through advanced authentication protocols, reduced manual workload for staff, and faster, more reliable access for authorized individuals.
Such integration not only fortifies security measures but also optimizes operational flow, making it an essential step for modernizing access control in various settings.
The Future of RFID in Access Control
The future of RFID technology in access control promises significant innovations. Anticipated advancements include improved encryption for heightened security, the fusion with biometric systems for multifactor authentication, and employing artificial intelligence for more intelligent access control decisions.
Additionally, the growing trend of the Internet of Things (IoT) is expected to integrate RFID systems with a wider array of devices and sensors, leading to more sophisticated and reactive security frameworks. These developments indicate a move towards more secure, efficient, and intelligent access control solutions.
These potential innovations not only promise to bolster security but also to elevate the user experience, making access control more intuitive and efficient.
Final Verdict
The adoption of sophisticated solutions like Lintechtt’s F3 card dispenser exemplifies modern advancement. These systems not only provide a more secure and efficient method for controlling access but also integrate seamlessly with various applications, elevating the overall functionality of security systems.
The transition to such advanced technology is essential for organizations looking to bolster their security infrastructure and adapt to the evolving demands of access management.